Security
UiPath Security
UiPath products make your company better while staying secure
Every UiPath product is designed and developed with security in mind.Security is built directly into our development lifecycle, by performing both automated security scans and penetration tests.We submit our releases to independent third-party review at the highest level to ensure that our security is more than trusted.
Security governance and controls
UiPath maintains a comprehensive information security management system and engages independent auditors to provide industry-standard certifications and attestations.
Additional details regarding the UiPath technical and organisational measures are available in UiPath Information Security Exhibit.
UiPath defines information security related roles and responsibilities across the organisation from the executive management (CISO, CPO, CTO, CLO) to employees and contingent staff.
Industry Certifications and Attestations
UiPath works to improve quality and security standards and design an internal roadmap of assurance and standards relevant to, and adequate for, the industry in which UiPath operates.
ISO/IEC 27001:2013, ISO/IEC 27017:2015, ISO/IEC 27018:2019
UiPath has engaged a certification body accredited by the ANSI National Accreditation Board (ANAB) and United Kingdom Accreditation Service (UKAS) to audit UiPath’s information security management system (ISMS) annually for conformity with the ISO/IEC 27001:2013 standard and aligned to meet the control implementation guidance and additional control sets of ISO/IEC 27017:2015 and ISO/IEC 27018:2019. The corresponding certification has been issued, the scope of which is detailed therein.
ISO 9001:2015
UiPath has engaged a certification body accredited by the ANSI National Accreditation Board (ANAB) to audit UiPath’s quality management system (QMS) annually for conformity with the ISO 9001:2015 standard and issue the corresponding certification the scope of which is detailed therein.
SOC 2®
AICPA System and Organization Controls (SOC) reports provide independent assurance to global customers in highly regulated industries who trust UiPath with their most sensitive data.
UiPath has engaged an independent certified public accounting firm to examine controls relevant to American Institute of Certified Public Accountants (AICPA) Trust Services Criteria for security, availability, and confidentiality relevant to the UiPath cloud offerings and issue SOC 2® reports.
Current SOC 2® Type 2 report covers the design and operating effectiveness of controls relevant to UiPath Automation Cloud Platform, Action Center, AI Center, Apps, Automation Hub, Automation Ops, Computer Vision, Data Service, Document Understanding, Automation Cloud Robots - VM, Automation Cloud Robots - Serverless, Insights, Integration Service, Process Mining Cloud, Orchestrator, Studio Web, Task Mining, Test Manager, and Communications Mining.
Health Insurance Portability and Accountability Act (HIPAA)
Under HIPAA, UiPath acts as a business associate to covered entities and other business associates. HIPAA attestation provides independent assurance to customers and business partners that UiPath has designed and implemented administrative, physical and technical safeguards applicable to UiPath’s business as a cloud service provider.
UiPath has engaged an independent certified public accounting firm to examine UiPath’s information security and privacy program every six months for conformity with applicable implementation specifications within the HIPAA Security, Privacy, and Breach Notification Rules.
Current HIPAA Type 2 attestation covers the design of applicable administrative, physical, and technical safeguards relevant to UiPath Automation Cloud Platform, Action Center, AI Center, Apps, Automation Hub, Automation Ops, Computer Vision, Data Service, Document Understanding, Automation Cloud Robots - VM, Automation Cloud Robots - Serverless, Insights, Integration Service, Process Mining Cloud, Orchestrator, Studio Web, Test Manager, and Communications Mining.
HITRUST HITRUST Risk-based, 2-year (r2) Certified status demonstrates that UiPath has met demanding regulatory compliance and industry-defined requirements and is appropriately managing risk. This achievement places UiPath in an exclusive group of organizations worldwide that have earned this certification.
Current HITRUST certification scope covers UiPath Automation Cloud Platform, Orchestrator, Insights, and Automation Hub.
National Health Service (NHS) Data Security & Protection Toolkit (DSPT) Self-assessment
UiPath UK Limited has submitted its 2022/2023 National Health Service (NHS) Data Security & Protection Toolkit (DSPT) self-assessment and exceeded standards. The DSPT allows organizations to measure performance against the UK National Data Guardian’s ten data security standards. Annual submission of the DSPT self-assessment provides assurance that UiPath is practicing good data security and that personal information is handled correctly.
Cyber Essentials Plus
Companies undergoing annual Cyber Essentials Plus audits help reduce the level of cyber security risk in the UK government supply chains. The Cyber Essentials scheme defines a set of controls which, when properly implemented, will provide organizations with basic protection from the most prevalent forms of threat coming from the internet. The scheme is mandatory for central government contracts advertised after 1 October 2014 which involve handling personal information and providing certain ICT products and services.
UiPath has engaged a certification body authorized by IASME to audit UiPath UK Limited and UiPath SRL annually against UK National Cyber Security Centre (NCSC) technical requirements for IT infrastructure and issue a Cyber Essentials Plus certificate.
Paris Call for Trust and Security in Cyber Space
UiPath joined a global call for Nation States, Companies and Civil Society to come together and face the increasing threats endangering citizens and infrastructure in cyberspace. It is based around nine common principles to secure cyberspace and the commitment to adopt responsible behavior. Discover the 9 principles here.
Bug Bounty Program
UiPath Bug Bounty Program aims to leverage the expertise of HackerOne's ethical hacker community to find vulnerabilities in our RPA Platform and surrounding ecosystem in order to keep our customers, partners and community users safe from malicious activities.
If you find a vulnerability on any systems that you feel are part of the UiPath organization, please send us an email at hackerone@uipath.com.
The Program focuses on high priority items such as:
Identifying and exploiting vulnerabilities in the implementation of Orchestrator and Robot that will permit escalation of privileges and perform out of rights/bound actions on Orchestrator.
Identifying publicly discoverable/accessible service end-points for UiPath.
Discovering management level secrets such as passwords.
Gaining control over the Orchestrator machine(s) in an on-premise scenario where the threat actor (malicious entity) is not a provisioned user on Orchestrator at application layer or OS level but is able to join the network on which robot and Orchestrator is deployed.
Using manual analysis or tools to conduct an objective evaluation of the Orchestrator application against OWASP Top 10 2017 Application Security Risks.
Injecting or uploading executable code into Orchestrator application that eventually runs itself, via interactive methods or access through APIs.
Internal & external testing
Before every GA/Major release for our products, we run:
Static Code analysis, 3rd Party Dependencies Vulnerability Scans, Dynamic analysis
3rd Party Dependencies scans - Licenses and Vulnerabilities
Anti-Malware Scans
Issues found go through a triage process and through a remediation process, as necessary.
Following testing and remediation, all UiPath products including official activity packages are code-signed by UiPath to provide authenticity and integrity. Partner and open-source packages included in UiPath offerings also go through the same testing, but are typically code-signed by their respective authoring body.
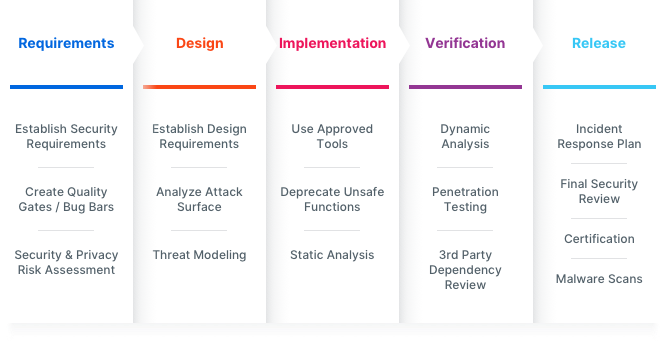
Security SDLC Tasks implemented as appropriate:
Explore other topics
Understand more about how we collect, use, disclose, share, and process data when people visit our website.
Find out moreRead the UiPath legal terms to find out more about the principles guiding your relationship with UiPath.
Find out moreDiscover our Global Partner Code of Conduct, our compliance standards, and our certifications and attestations.
Find out moreSubscribe to UiPath Trust Center updates
Receive announcements regarding security advisories, and legal or policy updates.