
Agentic automation in cybersecurity: richer context, informed response, faster resolution
Richer context means investigations start informed, not blind. Agentic automation pulls that context from your workflows and puts it in every alert.
Automate cybersecurity, unlock context, reach new heights in security and risk mitigation
The automation layer holds business context no security tool has ever had access to.
Data breach
$10.22M
average cost of a data breach in the U.S.
IBM, 2025
Infostealer malware
2.67M
machines infected by infostealer malware in early 2025
Kela, 2025
New malware
500k+
new pieces of malware are detected every day
Statista, 2025






Connect your security to automation workflows and unlock context for your SOC

Meet your security stack's most powerful ally: your automation layer
Hundreds of thousands of files flow through your automation workflows daily. See how business leaders are connecting that layer to their security stack, and what they unlock.
Better context leads to faster and sharper decisions
Your automation platform holds business context your security stack has never had. Connecting the two means every alert arrives richer, every investigation starts sharper.
Richer context per incident
Every alert carries context. No more starting an investigation from zero.
Precise responses, not just fast ones
Context turns detection into direction. Your team knows exactly what to do next.
Augment compliance automatically
Automate compliance reporting across ISO 27001, NIST, PCI-DSS, and CIS.
Your security stack finally has access to the automation layer. Explore the UiPath File Threat Detection and Response connectors.
Cybersecurity automation across the enterprise
From document ingestion to incident response, secure every touchpoint where threats enter your business.
- Threat-safe file processing
- Context-enriched detection
- Automated incident response
- Brute force mitigation
- Human-in-the-loop control
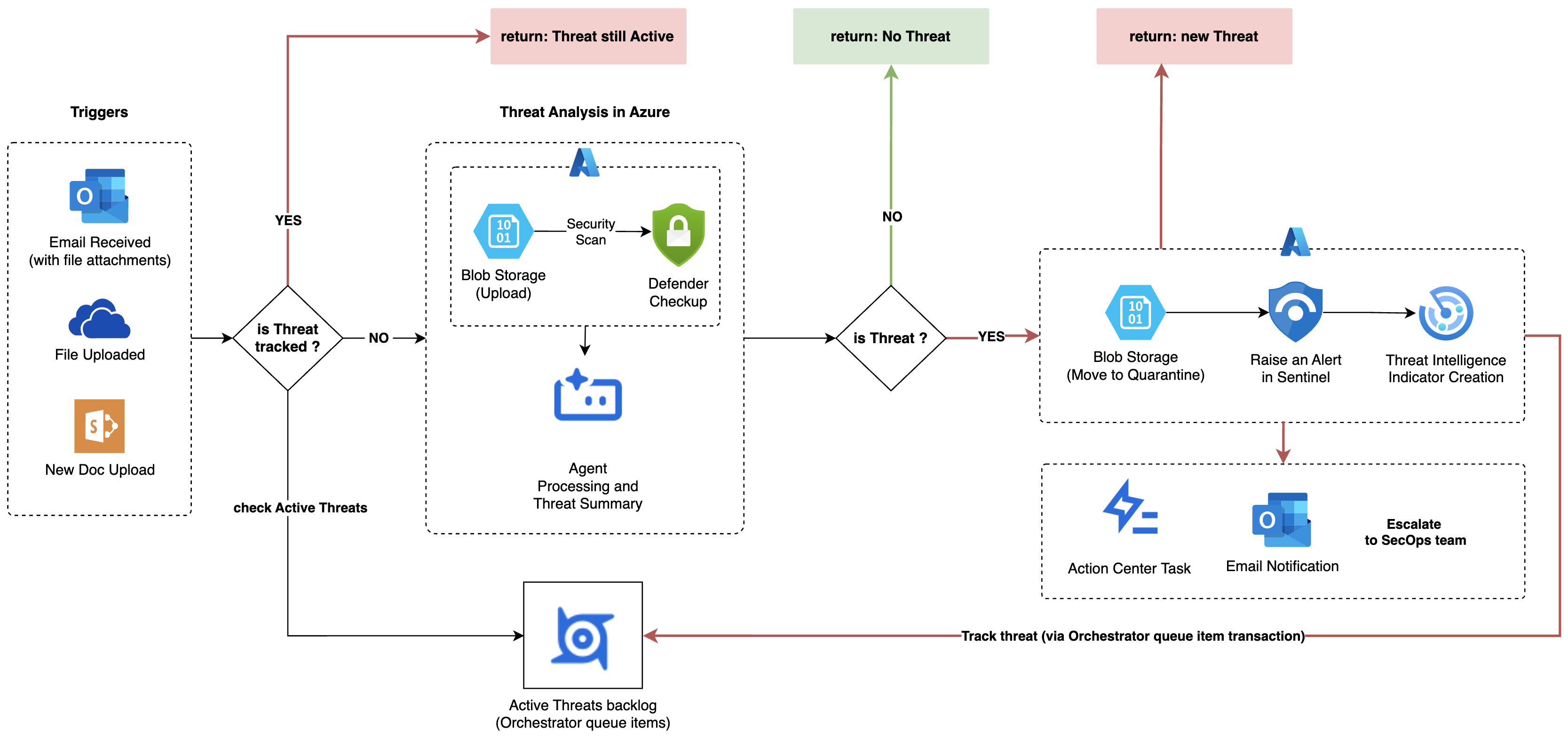
Every file entering your business is scanned for threats during the workflow
Every inbound file is scanned for malware and known threat signatures as part of the process run, not after. It does not matter where the file came from. Security runs alongside the workflow and flags threats before they reach production.

Scan results enriched with business metadata: workflow, source, team, transaction type
When a threat is detected, the alert already knows who sent the file and which workflow touched it. That business context comes from your automation layer, and no pure security tool has access to it.

Threats automatically trigger a context-rich incident response the moment they are detected
When a threat is detected, UiPath automatically handles everything downstream. The right incidents are raised and the right people notified, all carrying business-process context so your team can act on the first alert rather than investigate it.

Automated blocking of brute force attacks across your Azure infrastructure
Azure Security Center alerts on brute force attacks targeting VMs with public IPs. UiPath retrieves each alert, identifies the attacker's IP, and blocks it across all associated Network Security Groups automatically.

Automated response at scale, with human judgment exactly where it matters
Not every security decision should be fully automated. UiPath routes high stakes calls to the right people via Action Center, preserving human judgment without creating bottlenecks. The queue ensures every flagged file is reviewed exactly once and nothing slips through unresolved.

Explore cybersecurity automation resources

UiPath Connector for Microsoft Defender for Cloud
Find out how Microsoft Defender for Cloud connector enables UiPath to trigger and retrieve results from automated security scans.

UiPath Connector for Microsoft Sentinel
Find out how UiPath automations can create, update, list, modify, close, and enrich security incidents in Sentinel.

UiPath Connector for threat intelligence Connector
Find out how the connector integrates UiPath’s automation with sentinel threat intelligence, allowing it to publish threat indicator.

